As if we all don’t have enough to think about during the coronavirus pandemic, there has been a growing wave of opportunistic cyberthreats to contend with as well.

There have been attacks on services like Zoom, as well as a growing number of phishing attacks.
The following are cybersecurity tips to following during coronavirus.
Zoom and Cybersecurity
Zoom was one of the big names during the early days of the U.S. coronavirus pandemic because it was a tool that facilitated online work and learning. It’s still a top pick for many organizations, but the video conference platform did face some security issues.
There was evidence that people were breaking into Zoom chats and chats were becoming available online. New York City banned schools from using Zoom for remote learning, and Google doesn’t let employees use it on their work laptops either.
Following a few high-profile incidents, Zoom CEO and Founder Eric Yuan did apologist to users, and in the months since those, there has been a big push by the company to improve cybersecurity protections.
Phishing Attacks
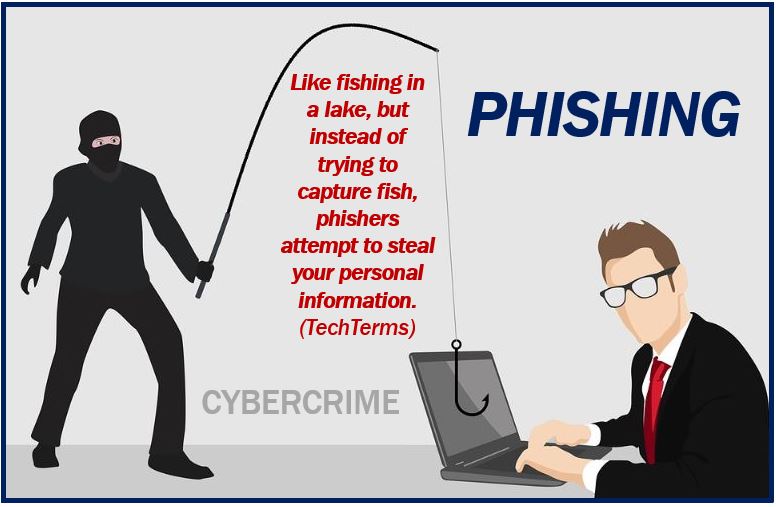
Phishing attacks are certainly not new, but they do continue to be a number one way attackers target people. They just found new avenues with coronavirus. Phishing attacks occur when a cybercriminal sends an email, and they claim to be from a legitimate organization.
Within the context of coronavirus, they might say that you need to click on an email attachment to see updated virus statistics, just as an example. If you click an attachment or embedded link, you will then download malicious software onto your computer or device.
The malicious software is known as malware.
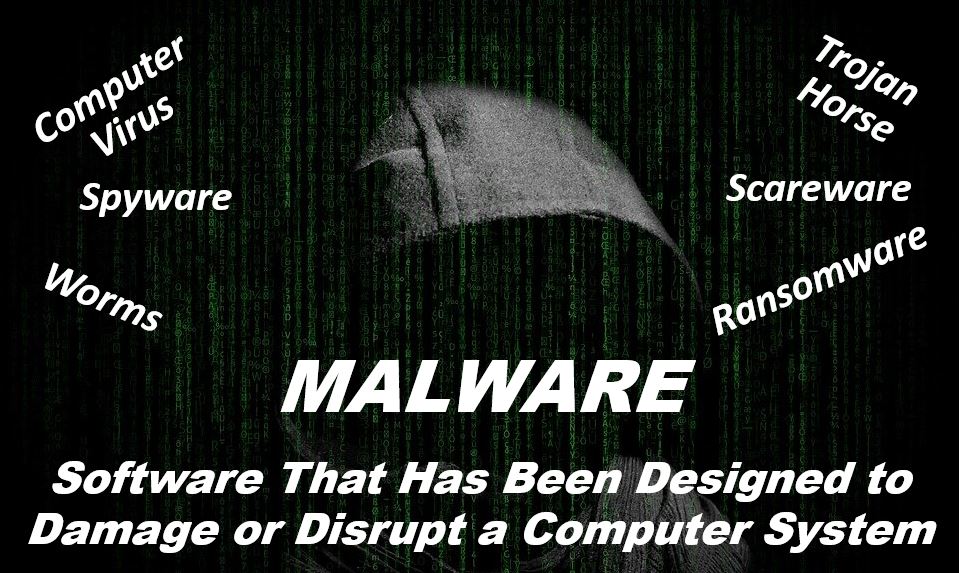
Once you download that malware, it can take control of your computer and then steal your financial information.
One popular route cybercriminals take is pretending to send emails from the Centers for Disease Control and Prevention. There might be a link to what the email says are cases in your area.
Another scam could come in the form of an email with health advice.
To avoid phishing emails, first, always check the email address or link. If it’s a link, hover your mouse over it to see where it goes. You also need to keep in mind that email addresses used by phishers may look very similar to actual emails. If you notice a suspicious email, delete it.
Also, look out for generic greetings and spelling mistakes.
No email should ask for your personal information or have anything you need to do urgently, either.
Contact Tracing Scams
A newer type of scam that isn’t exactly cybersecurity-related, but is similar, takes advantage of contact tracing. Contact tracing is how local governments are identifying people who have been in contact with someone who has covid-19. Contact tracers will give them quarantine instructions and check in to monitor their symptoms.
These people usually work for the state department of public health, and they’ll try to get the contact information of anyone an infected person may have come in contact with.
Be aware in these situations that a contact tracer isn’t going to ask for information like your Social Security Number or any financial information.
You might receive a phone call or a spam text message that asks you to click a link similar to phishing emails.
In general, whether now or in the future, there are certain things you can do to protect yourself against online and phone-based scams. One important thing is to learn how to recognize phishing and to be careful and cautious about every single email you receive, especially if it’s asking you to take any kind of action.
Again, even those these scams seem simple, they’re often very effective, which is why they continue to be used.
Beyond that, make sure your online accounts are protected with multi-factor authentication. This means that you have to input two or more credentials to log in.
You should also make sure that you have your automatic updates enabled on all your devices, if possible. When you do this, it makes sure that your apps and your entire device get the security patches it needs, which will help protect you if you are the victim of a malware attack.
You need to make sure that you’re regularly backing up all of your data, too, because there are ransomware attacks that can occur. In these attacks, hackers can take over your device and they demand payment to give you access to it again.
Unfortunately, it’s not uncommon for criminals to take advantage of already challenging situations, like the one we’re in now.
Interesting related article: “What is a Scam?“

