What is cyber security? Definition and examples
 Cyber Security refers to the practice of protecting computer systems, networks, programs, and data from cyber attacks or digital attacks.
Cyber Security refers to the practice of protecting computer systems, networks, programs, and data from cyber attacks or digital attacks.
The word cyber is short for cybernetics. Cyber is a prefix or adjective which means relating to or characteristic of IT (information technology), computers, and virtual reality. Cybernetics is the science of communications and automatic control devices or machines, as well as living things. Cyber originated in the early 1980s as a short form for cybernetics.
Therefore, cyber security refers to anything that protects computers, information technology, virtual reality, etc.
Cyber security is part of the umbrella term Information Security. Information security or IT security aims to protect all digital and hard copy information assets.
Given the pervasive nature of cyber threats, it’s crucial for cyber security to evolve continuously, integrating the latest advancements in artificial intelligence and machine learning for better threat detection and response.
Spelling
We can write the term as one or two words – “cyber security” or “cybersecurity.”
Cyber security – protection from cyber attacks
New technology is forever trying to protect computers and systems from hackers, cyber attacks, and malware threats. A cyber security kiosk can help companies safeguard their infrastructure from malware threats on removable devices brought in by employees, contractors, and others.
A cyber attack is any type of offensive maneuver that targets a computer network or computer information system. We can write the term as one or two words, with or without a hyphen, i.e.:
- cyber attack,
- cyber-attack, or
- cyberattack.
However, you should select one of the three writing options and stick to it throughout the text.
Cyber attacks may also target personal devices, infrastructure, and medical devices. Tablets, smartphones, and laptops, for example, are personal devices.
A cyberattack that targets infrastructure can devastate a whole town, region, or even country. Our electricity network, railway systems, and water supply are examples of infrastructure. Any attack that leaves thousands or millions of people without electricity, natural gas, or water could result in deaths, especially during wintertime.
Cyber security is all about making sure our infrastructure, personal devices, medical devices, etc. continue operating unhindered.
The most common way cybercriminals access confidential information today is by phishing. They send emails pretending to be from legitimate companies. The email has a malicious attachment or link to a fake website.
Cyber attackers
 The person who carries out a cyber attack – a cyber attacker – has malicious intent. This person intends to cause harm. Cyber attackers are invariably breaking the law when they initiate an onslaught. They aim to steal, destroy, or alter something by hacking into a network or computer system.
The person who carries out a cyber attack – a cyber attacker – has malicious intent. This person intends to cause harm. Cyber attackers are invariably breaking the law when they initiate an onslaught. They aim to steal, destroy, or alter something by hacking into a network or computer system.
According to CISCO, an American multinational tech company, cyber attackers usually aim to destroy, change, or access sensitive information. They may do this to interrupt normal business operations or extort money from people, businesses, governments, and other organizations.
Regarding cyber security, CISCO makes the following comment:
“Implementing effective cyber security measures is particularly challenging today because there are more devices than people, and attackers are becoming more innovative.”
Cyber security – people, processes & technology
For effective cyber security in any organization, its people, processes, and technology need to complement one another. Without these three parts working properly and together, an effective and successful defense from cyber attacks is more difficult to achieve.

-
People
Everybody in an organization needs to understand and adhere to fundamental data security protocols. For example, data should be backed up, email attachments should be treated with extreme caution, and passwords should be robust.
-
Processes
All businesses, government departments, and other organizations should have cyber attack measures in place. In other words, a framework for both successful and attempted attacks. Everybody should know what to do if they suspect that an attack is taking place or has occurred.
-
Technology
All smart devices, routers, computers, medical devices, etc. should be protected. Today, we have DNS filtering systems, next-generation firewalls, antivirus software, and email security solutions which make it significantly more difficult for hackers to find a way in.
In addition to defensive measures, proactive cyber security strategies involve regular audits and simulations to anticipate and mitigate potential threats.
Cyber security market
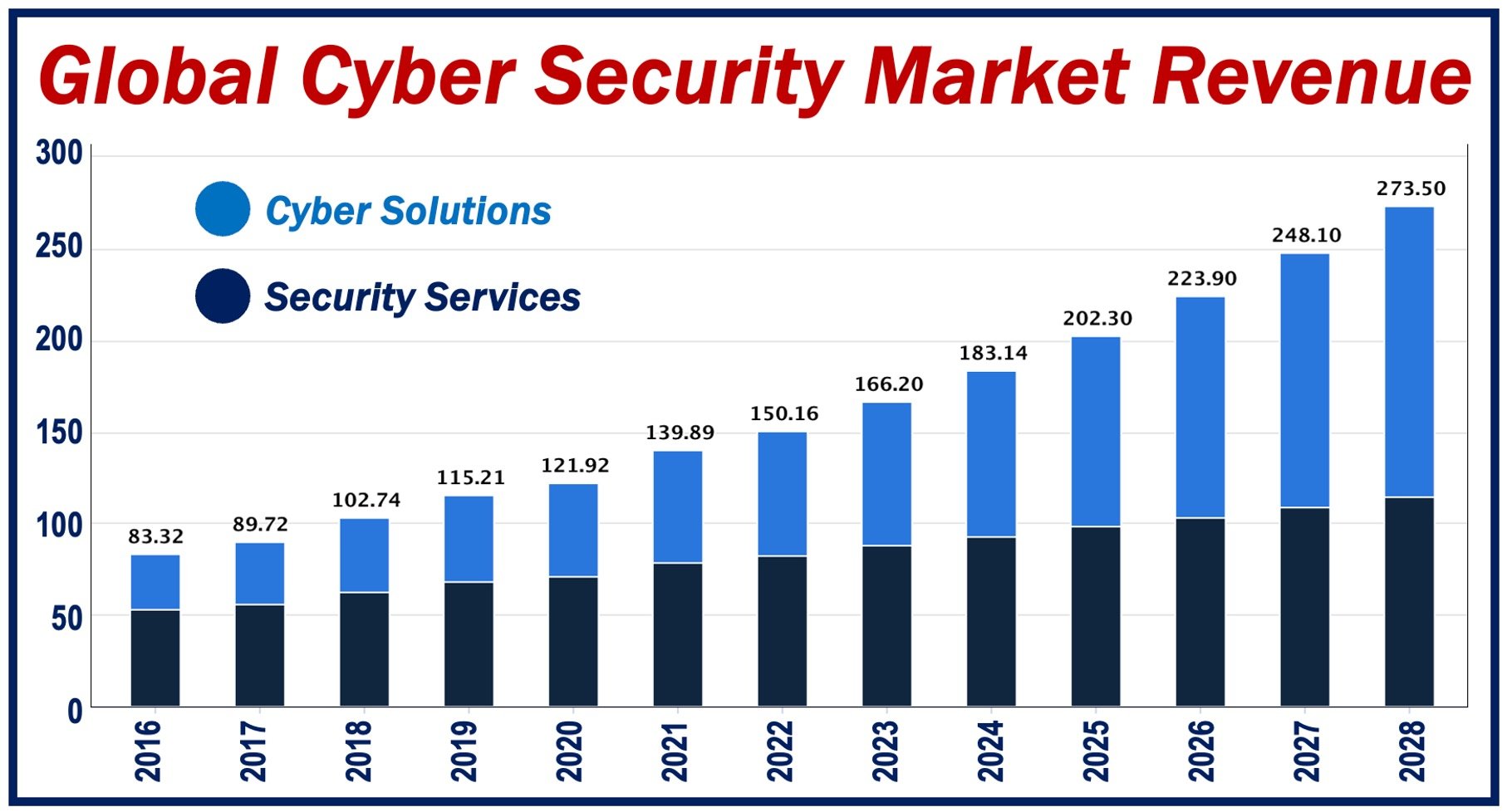
According to statista.com, the cyber security market reached $166 billion in 2023. Security services, at $87.97 billion, dominated the market in 2023.
Revenue is forecast to grow annually (CAGR 2023-2028) at 10.48%, reaching $273 billion by 2028.
Video – What is Cyber Security?
This interesting video, from our sister channel on YouTube – Marketing Business Network, explains what ‘Cyber Security’ is using simple and easy-to-understand language and examples.

