Your IT infrastructure grows every day, and you know it! Each day, you add new users and IT assets – hardware and software. It’s the job of the system admins to manage and track these assets using an inventory system. This allows you to easily resolve potential IT issues. With better IT admin support, you can access all the assets that exist in the organizational IT landscape – data center, network, remote sites, user workstations, and more.
What is an IT Inventory System?
An IT inventory system is a set of business practices that provide simple and clear inventory management of software, hardware, licenses, contracts and purchase orders, and consumables. It also provides a real-time view of assets under management. It allows you to join contractual, financial, and inventory functions to support the life cycle management and strategic decision-making for the IT inventory. With this system, you can get the maximum value from the use of the assets, optimize inventory purchase strategies and decisions, and right-size IT inventory.
An IT inventory system allows you to see your IT infrastructure inventory and helps you gain an in-depth knowledge of the following:
- Which systems and equipment exist
- Where the components are located
- How to use them
- How much they cost
- When they were added to the inventory
- If they have an expiration date or not
- How they affect IT and business services
This level of visibility into the asset details can help your organization to improve infrastructure performance and efficiency, and to minimize overhead expenses related to the performance. All organizations use IT inventory systems, in one way or the other. You need to use an inventory system intelligently to achieve IT operational efficiency, simpler auditing compliance, financial accountability, and long-term asset maintenance and manageability.
How does an IT Inventory System Work?
An IT inventory system establishes a centralized asset repository that records the presence and purchase of all hardware and software inventory. Here’s how it works:
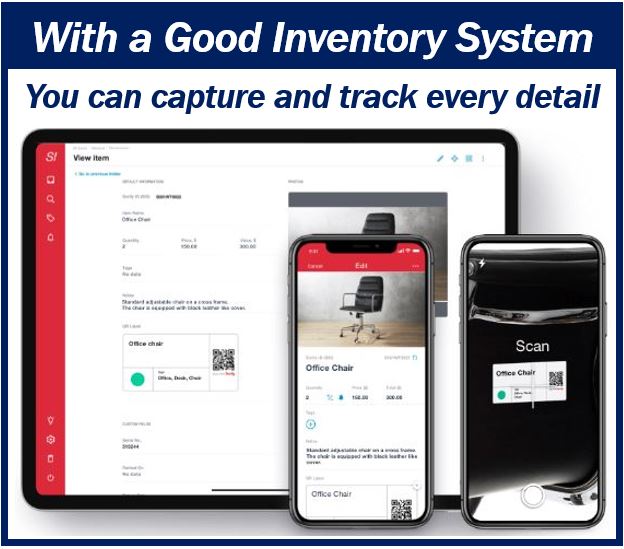
It starts with asset discovering, capturing, and storing. During this process, it discovers all hardware and software components of the IT inventory on the infrastructure. It also captures all their details, including the type of asset, specifications, etc. And then, it stores them in the asset repository.
Asset tracking follows, where it identifies and tracks the increase or decrease in the number of assets, and the changes in the location of the assets. It also tracks the assignment status and user information.
In the asset lifecycle management, it lets you capture the asset lifecycle data directly from requisitioning, assignment and purchase, to decommissioning and expiry.
It ends with asset reporting and alerting. It generates asset inventory reporting, which allows you to receive alerts regarding asset warranty and lease expiration.
Centralized organization-wide inventory management and asset repository help you support various functions, including incident management, configuration management, problem management, and service level management. In building a centralized asset repository, you need to understand its difference from the configuration management database.
Why do You Need an IT Inventory System?
Below are several reasons why your company needs to use an IT inventory system:
Automated Asset Discovery and Tracking
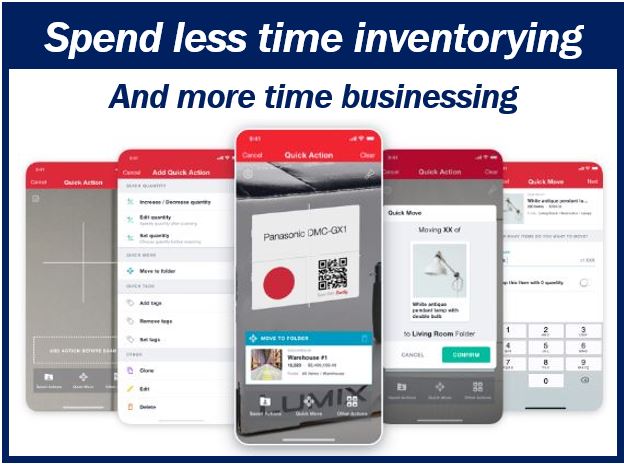
A lot of organizations manage their IT asset inventory using paper-intensive processes, but this can greatly drain resources. These are also highly prone to inconsistencies and inaccuracies. In this process, users often use Spreadsheets, where they enter the details of the assets, and then constantly modify them as they update. With the introduction of IT inventory systems, you don’t have to worry about this anymore. You will be able to make this process simpler and quicker.
Gaining control over IT inventory
With an IT inventory management system, you’ll be able to easily view the hardware and software components of a server, computer, or any network infrastructure. It also gives you better IT administration control and accountability.
If you use an automated asset discovery, along with management functionality and other application monitoring tools, you’ll be able to see the computer inventory details. You’ll also be able to find out if your employees are using unauthorized or non-compliant software or hardware in their workstation.
Procurement Forecast and Strategic Inventory Planning
If you track the inventory you have in your IT infrastructure, it becomes easier to plan for your future spending on assets. If you don’t know what currently exists in your end-user systems, it will be hard to plan on the procurement budget. You may need to procure more assets, even those that are unnecessary.
With the help of centralized and streamlined asset management, you can scan your entire network and list which software and hardware your system is using. This will allow you to plan well in advance for future asset needs, to maximize the existing asset utilization, and eliminate unnecessary expenses.
Asset Lifecycle Management
An IT inventory system will allow you to keep track of information, such as the date when your company purchased the hardware, how long you have been using them, if there’s a lease expiring on the components, etc.
System administrators need to know the software version, and how long the end-users have been running it on their system, and whether their OS is current or not. Knowing all these will help them decide whether they should replace the old hardware or not, update the firmware on the system, patch or uninstall a vulnerable application, and more.
Vendor contract management should be familiar with asset information so they will know when to renew or extend a contract with the vendor or software/hardware provider, based on the contract, purchase order, and expiration dates.
Increased Accountability
Tracking your IT inventory and updating it using inventory management systems will help you monitor your computer hardware and software. And as a company, you must ensure compliance with corporate security policies, and you’ll be able to achieve this using an IT inventory system.
If you allow system admins to isolate vulnerabilities quickly, such as unauthorized or illegal software, outdated software, malicious and unauthorized downloads, it’ll be easier to see where the potential risks exist. You’ll be able to prevent these risks before major problems could arise.
_______________________________________________________________________
Interesting related article: “What is Information Technology?“

