What is a watering hole attack? Definition and examples
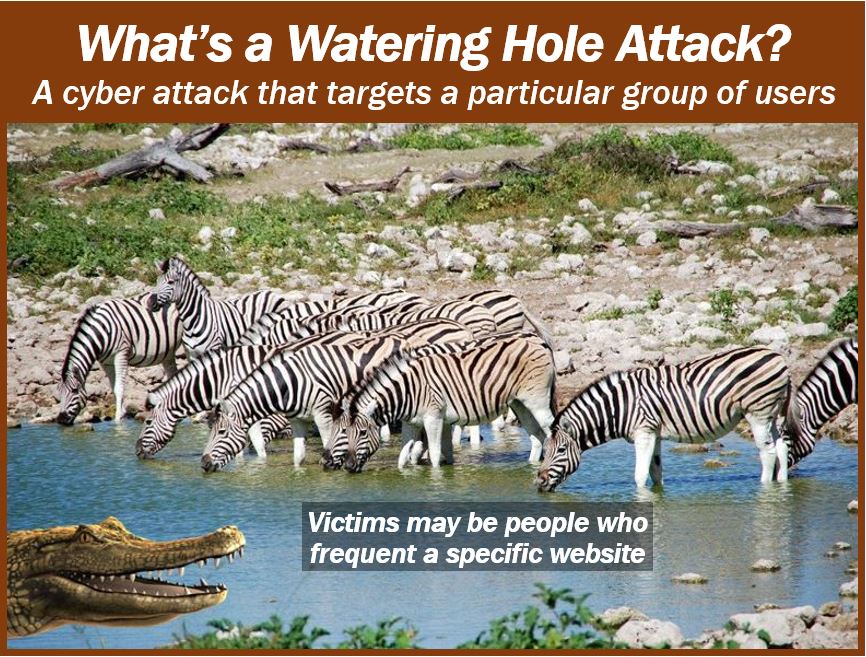
A Watering Hole Attack /ˈwɔːtərɪŋ-həʊl əˈtæk/ makes us think of crocodiles grabbing impalas or zebras while they are drinking. It does mean that, but in the world of cybersecurity, it also refers to attacking visitors to a specific website.
In a watering hole attack, hackers load malicious malware onto a website. When visitors come to that site, the malware surreptitiously makes its way into their computer systems. Imagine that the visitors are the zebras or impalas and the website they come to is a watering hole – hence the name.
Wikipedia has the following definition of the term:
“A computer attack strategy, in which the victim is of a particular group (organization, industry, or region). In this attack, the attacker guesses or observes which websites the group often uses and infects one or more of them with malware.”
“Eventually, some member of the targeted group becomes infected.”
If a hacker is seeking specific data, he or she will target users that go to certain IP addresses. They lie in wait for an opportunity to pounce on their unsuspecting prey at the website or watering hole.
Setting up a watering hole attack
So, how do these hackers identify the websites that specific user groups visit? Users, in fact, unwittingly provide them with this data when they go online and surf the net. They gather and analyze data from marketing and advertising automated tracking services to access traffic patterns.
The best websites to target are those of smaller blogs or companies because of their relatively lower cybersecurity compared to their larger counterparts.
They plant a malware code and wait. Over time, a growing number of visitors become their unsuspecting victims. Watering hole attacks have an extremely high success rate.
Victims are completely defenseless
When they visit the target website, users walk straight into the hacker’s trap. They don’t have to click on anything to download the malicious code, which runs in the background automatically.
With the malware in the victim’s computer system, the attacker can scan their device for confidential data such as banking passwords and usernames, IP information, and personal details.
A watering hole attack can sometimes affect tens of thousands of individuals in a very short time, especially if the target website is a popular one.
If you want to minimize your risk of becoming a victim of a watering hole attack, make sure you regularly update your software.
TechAdvisory.org offers the following advice:
“To detect watering hole attacks, you must use network security tools. For example, intrusion prevention systems allow you to detect suspicious and malicious network activities.”
“Meanwhile, bandwidth management software will enable you to observe user behavior and detect abnormalities that could indicate an attack, such as large transfers of information or a high number of downloads.”
Additionally, educating employees about the risks of watering hole attacks and promoting safe browsing habits can significantly reduce the likelihood of such attacks succeeding.
Organizations should also implement comprehensive cybersecurity strategies, including regular security audits and updates, to create multiple layers of defense against such sophisticated cyber threats.
Two Videos
These interesting videos, from our sister channel in YouTube – Marketing Business Network, explain what a ‘Watering Hole Attack’ and ‘Cybersecurity’ are using simple and easy-to-understand language and examples.
-
What is a Watering Hole Attack
-
What is Cyber Security?

