A new data-stealing malware has been targeting Facebook users in the latest phishing scheme known as Ducktail.
According to DarkReading, “As Ducktail hijacks Facebook business accounts by gaining administrator-level access, it essentially gives the threat actor the ability to gain unlimited access to use the hijacked business account as they wish. This could include carrying out malicious advertising (malvertising), classic fraud efforts (running scams), or to spread disinformation. The threat actor could also potentially use its newfound access to blackmail a company by locking them out of its own business account.”
This incident is a reminder for companies to strengthen their overall cybersecurity from attacks that target humans — social engineering attacks.
How can companies defend their most valuable assets from it?
As Warren Buffett said: “It’s good to learn from your mistakes. It’s better to learn from other people’s mistakes.”
Let’s start with what we know so far about the latest Facebook phishing scheme to determine what other businesses can learn from it and apply it to their overall social engineering attack prevention.
Facebook Ad Phishing Scheme Explained
Here, we’re talking about the new version of the Ducktail malware created by a group of Vietnamese hackers.
Although they’re known for their Facebook operations, their previous campaign took place on LinkedIn, where they targeted users with similar information stealing malware.
During these LinkedIn attacks, the group obtained information concerning multiple Facebook business accounts.
The primary targets of the latest Ducktail phishing campaign are users that manage Facebook Business accounts. Companies that have been relying on Facebook ads to promote their businesses are known victims of this group that tried to hijack their accounts.
To lure Facebook users to click on malicious links, the malware has been posing as an opportunity to get applications or other supposedly cracked software for free — including Telegram and a variety of games.
Those that fell for the phishing scheme installed malware that can access the data linked to Facebook accounts, but also any other private information stored in the browser.
That could include information regarding crypto wallets, all about the system, user accounts, and more.
As with most scams, this phishing campaign is financially motivated.
The final goal of the malware has been to access financial information, such as details concerning PayPal accounts.
Safety Tips For Facebook Users
In order to protect accounts, users should start with these precautions:
- Use strong passwords that are regularly changed (every three months)
- Rely on private browsers
- Avoid entering sensitive data in the browser
- Install reliable anti-malware and antivirus programs
The first tip is to have a strong password that can’t be easily cracked. It should have over 10 characters that are a combination of versatile numbers, letters (both uppercase and lowercase) as well as symbols.
Next, it’s best to switch to a private browser. If you work in incognito mode, the browser will not remember or store the data that you’re using to log into your accounts.
Therefore, even if you happen to click on a malicious ad, they’ll have a difficult time going down the data rabbit hole that would allow them to access more and more information saved within the browser.
Don’t store private information in the browser.
Namely, in the phishing attack on LinkedIn, threat actors have written malware that could gather data about business accounts stored in the browser.
While a business needs a layered security system that consists of a variety of tools that protect the infrastructure of the business and cover all devices and software used in everyday work, start with reliable antivirus and anti-malware to guard the information.
Even if the new types of malware are created in a way that they can bypass the antivirus, they will still block certain activities, such as attempts at accessing the website that the software concluded is not safe.
Preventing Social Engineering Attacks
Social engineering attacks such as phishing are prevalent now more than ever. Therefore, it’s not a question of if but when it will occur within your organization.
-
How to prevent them
Start with some basic cybersecurity training for your teams that teaches them how to recognize as well as respond to different types of phishing threats.
While this is a good start, since most data breaches are caused by human mistakes, employee awareness training on its own is not enough. Introduce protocols, policies, and cybersecurity tools as well to the anti-phishing arsenal.
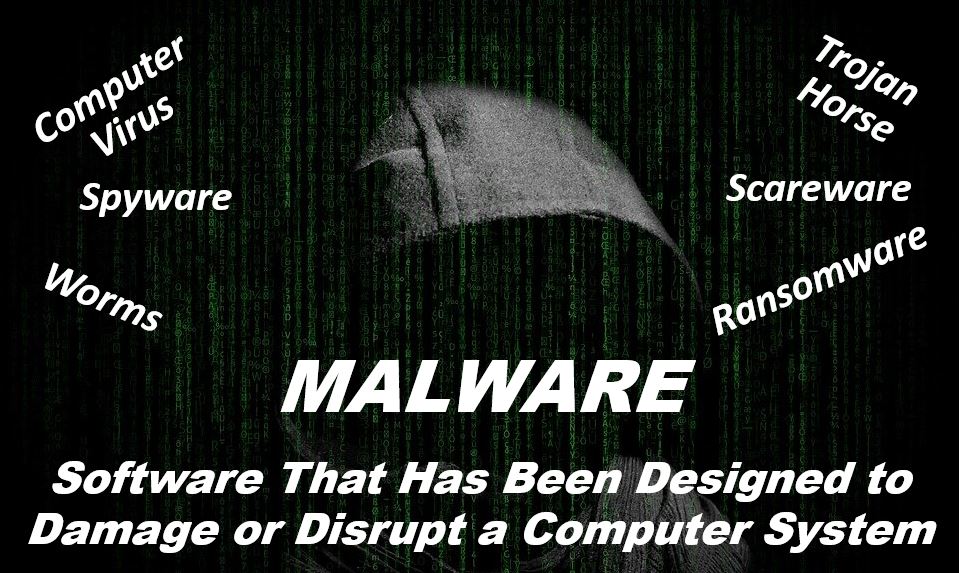
As was the case of the Ducktail Infostealer, these phishing attacks come with malware. To successfully defend against such phishing threats, a good defense should include a reliable antivirus program.
Considering that new types of viruses can bypass regular anti-malware, it’s necessary to continually monitor and seek the signs of suspicious activity.
Ducktail malware is designed to go under the radar of most antivirus software. To achieve that, it would upload the malicious file to a legitimate hosting service and load only in the memory.
Besides having both anti-malware and antivirus software, additionally strengthen your security with:
- Multifactor authentication — that prevents hackers from accessing the system using compromised credentials
- Duty separation — high-risk activities such as money transfers should require more than one sign-off from different employees
- Improved email security — most have basic filters that send suspicious emails right to the spam folder. Also, introduce advanced email security that can identify sophisticated phishing attempts
Key Takeaways
Phishing is one form of social engineering attack we’ll keep hearing about.
The main reason why it’s difficult to weed it out is that it attacks the weakest link in the security of any system — humans. It puts pressure on them or relies on their mistakes.
Another issue is that threat actors are continually changing their techniques as well as altering the malware that follows social engineering attacks. New versions are more difficult to detect by traditional cybersecurity tools.
The consequences of data-stealing malware such as Ducktail are severe.
The information that hackers obtain can get them unauthorized access to business accounts and enable them a deeper lateral movement in the organization or access to sensitive information they can either leak or use for identity theft.
Therefore, having strong email filters, a reliable antivirus program, introducing employee training, multifactor authentication, and separating duties is a great start for avoiding the financial damage that comes with potential social engineering attacks.

